2FA TOTP without crappy authenticator apps
Last modification on
This describes how to use 2FA without using crappy authenticator "apps" or a mobile device.
Install
On OpenBSD:
pkg_add oath-toolkit zbar
On Void Linux:
xbps-install oath-toolkit zbar
There is probably a package for your operating system.
- oath-toolkit is used to generate the digits based on the secret key.
- zbar is used to scan the QR barcode text from the image.
Steps
Save the QR code image from the authenticator app, website to an image file. Scan the QR code text from the image:
zbarimg image.png
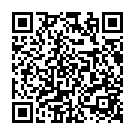
An example QR code:
The output is typically something like:
QR-Code:otpauth://totp/Example:someuser@codemadness.org?secret=SECRETKEY&issuer=Codemadness
You only need to scan this QR-code for the secret key once. Make sure to store the secret key in a private safe place and don't show it to anyone else.
Using the secret key the following command outputs a 6-digit code by default. In this example we also assume the key is base32-encoded. There can be other parameters and options, this is documented in the Yubico URI string format reference below.
Command:
oathtool --totp -b SOMEKEY
- The --totp option uses the time-variant TOTP mode, by default it uses HMAC SHA1.
- The -b option uses base32 encoding of KEY instead of hex.
Tip: you can create a script that automatically puts the digits in the clipboard, for example:
oathtool --totp -b SOMEKEY | xclip